Introduction
How Power BI Ensures Security?
Why do we need Security in Power BI?

1. Keeps Out Unauthorized Access:
2. Makes Sure Your Data Stays True
3. Follows the Rules
Understanding Power BI User Permissions
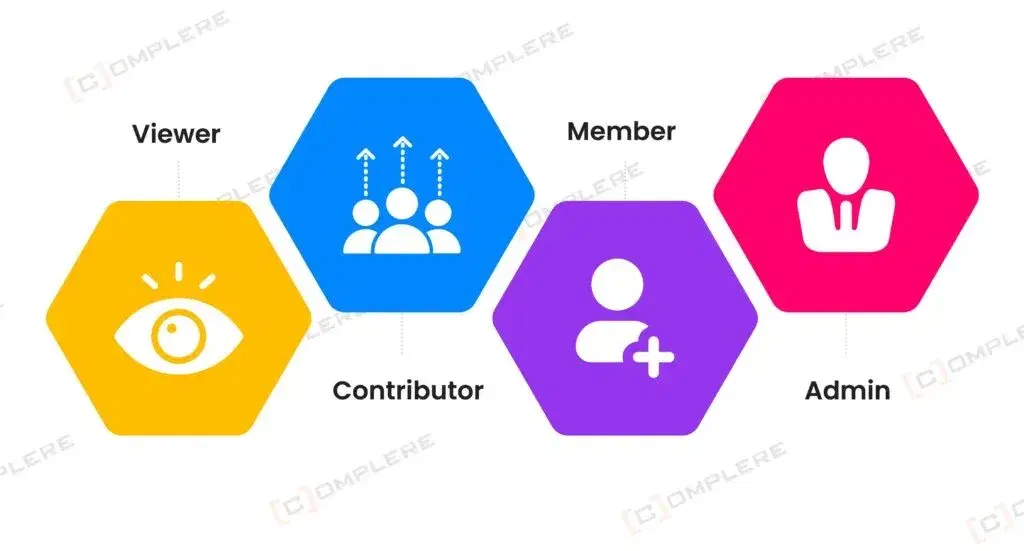
- Viewer: This permission allows the visitors to just see your valuable business data. They cannot change anything.
- Contributor: This specific permission of Power BI allows contributors to just shift your data from one place to another for better management. But contributors cannot open or edit your business data.
- Member: People who come with membership code can easily enter and invite others also. They can edit or can make changes to your data as well.
- Admin: The organizer has full access. He/she can control everything. He will take the decision for who can get in, who can contribute, and who comes in the member category. Admin controls the overall Power BI environment.
Explaining Power BI and Data Protection
- Row-Level Security: Power BI effectively protects your data by providing categorized access at the place of providing full access of restricting full access. RLS makes sure users see or use only the data rows they are allowed to.
- Data Encryption: This highly advanced feature of Power BI Security assures that your data will remain safe whether it is at rest of in transit.
- Audit Logs: Power BI maintains proper record of each login. It provides a well-maintained data of the whole track of authorized entries and unauthorized attempts for entry.
Improve Your Defenses with the best Power BI

Governance in Power BI: Beyond Permissions
- Workspace Management: Organize reports based on business units or use cases
- Data Cataloging: Tag and document datasets to reduce duplication
- Lifecycle Policies: Apply versioning, archiving, and retention policies
- Usage Monitoring: Use built-in dashboards to track who’s viewing and editing reports
Integrating Power BI with Microsoft Defender and Azure
- Defender for Cloud Apps: Flags unusual data access behavior and provides real-time alerts
- Azure Information Protection (AIP): Allows data classification, labeling, and usage rights
- Azure Purview: Helps catalog and govern data sources beyond Power BI














